Multifactor authentication
This is not a complete article: This is a draft, a work in progress that is intended to be published into an article, which may or may not be ready for inclusion in the main wiki. It should not necessarily be considered factual or authoritative.
Multifactor authentication (MFA) allows you to protect your account with more than a password. Once your account is enrolled in multifactor authentication, you will be prompted for a second action in addition to your password. This action could be accepting a notification on your phone (Duo Push), entering a 6 digits time based code, entering a single-use bypass code, or pushing on the button of a Yubikey hardware key. This second factor will be required when connecting to many of our services. Note that while we are deploying this, not all of our services may supported it, but our goal is to protect most of our services with mutlifactor authentication in the near future.
Registering factors[edit]
Registering multiple factors[edit]
When you enable mutlifactor authentication for your account, we strongly recommend that you configure at least two options of second factor. For example, you can use a phone and single-use codes, a phone and a hardware key, or two hardware keys. This will ensure that if you lose one factor, you can still use your other one to access your account.
Using a smart phone or tablet[edit]
When using a smart phone or tablet, you will first need to install the Duo Mobile authentication app. You can find it on the Apple Store, or on Google Play. Once the application is installed, visit the multifactor authentication management page in your account. On that page, select the Duo Mobile option, give a name to your device, then scan the QR code that is shown to you.
Using a YubiKey hardware key[edit]
YubiKeys are hardware tokens made by the company Yubico. They have the size of a small USB stick, and different models support different ports. Some will connect to a USB-A port, USB-C port, Lightning. Some models also support near field communication (NFC) to be used with your phone or tablet. To figure out which one may best suite your need, consult this page. They cost between 50$ and 100$, and they are the best option if you do not want to use or if you do not have a smart phone. They are also the best option if you are often in situations when using your phone is not possible.
YubiKeys support multiple authentication protocols which are commonly used for web authentication, such as WebAuthn, FIDO2, U2F. However, the one protocol which works with SSH connections used on our clusters is called Yubico One Time Password (OTP). When using Yubico OTP, pressing the button on the key will write a long string of characters looking like vvcccbhbndkglanfhevnricjdvftcfugdtjeflgrhenr, which will act as your second factor.
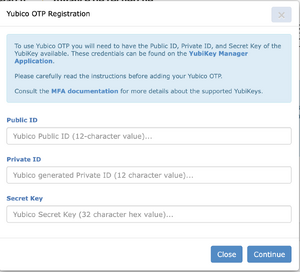
Yubico OTP itself has two modes which it can use. In Yubico Cloud mode, authentication requests are forwarded to Yubico's cloud, in which your key is already pre-registered when you purchase it. This mode is not supported by Duo, which instead supports Yubico OTP. For this mode, you need to have the Public ID, the Private ID, and the Secret Key for your key. If you already have this information, you can use your existing information to register your Yubico OTP on your mutlifactor authentication account page. If you do not have this information, you need to configure your key using the steps below.
Configuring your YubiKey for Yubico OTP[edit]
To configure your Yubikey, follow the instructions below:
- Download and install the YubiKey Manager software from the Yubico website.
- Insert your Yubikey and launch the YubiKey Manager software.
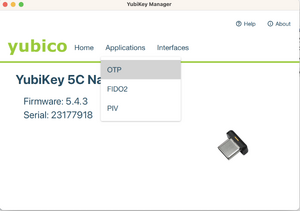
- In the YubiKey Manager software, select Applications, then OTP
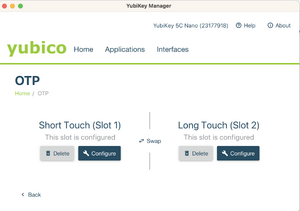
- Select Configure for either slot 1 or slot 2. Slot 1 corresponds to a short touch, while slot 2 is a long touch on the key. Slot 1 is typically pre-registered for Yubico Cloud mode. If you are already using this slot for other services, either use slot 2, or click on Swap to transfer the configuration to slot 2.
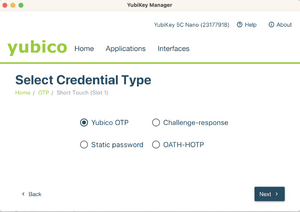
- Select Yubico OTP
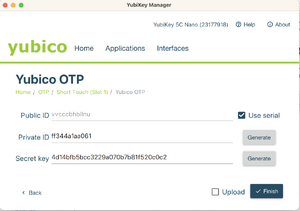
- Select Use serial, then generate a Private ID and a Secret Key. Securely save a copy of the data in the Public ID, Private ID, and Secret key fields before you click Finish, as you will need the data for the next step.
- Keep the previous screen open and log into the CCDB to register your Yubikey in your mutlifactor authentication account page
Using your second factor with SSH connections[edit]
When your account has multifactor authentication enabled, if you connect to a cluster which supports it via SSH, you will be prompted to use your second factor after you first authenticate either using your password or your SSH key. This prompt will look like this:
[name@server ~]$ ssh cluster.computecanada.ca
Duo two-factor login for name
Enter a passcode or select one of the following options:
1. Duo Push to My phone (iOS)
Passcode or option (1-1):
At this point, you can either select which phone or tablet (if you have multiple devices enrolled, you would get a list) you want Duo to send a notification to. You will then get a notification on your device, which you need to accept or decline.
If you are using a Yubikey, a backup code, or if you prefer to enter the time based one time password that the Duo Mobile application shows, you would write these instead of selecting an option. For example:
[name@server ~]$ ssh cluster.computecanada.ca
Duo two-factor login for name
Enter a passcode or select one of the following options:
1. Duo Push to My phone (iOS)
Passcode or option (1-1):vvcccbhbllnuuebegkkbcfdftndjijlneejilrgiguki
Success. Logging you in...
Configuring your SSH client to only ask every so often[edit]
You can configure your OpenSSH client to only ask for the second factor every so often by using the "ControlMaster" mechanism. To do so, edit your .ssh/config to add the lines:
Host HOSTNAME
ControlPath ~/.ssh/cm-%r@%h:%p
ControlMaster auto
ControlPersist 10m
where you would replace HOSTNAME with the host name of the server for which you want this configuration.